Hackers are always targeting medical technology due to the fact that medical databases and equipment have a lucrative wealth of private data in the lives of people looking for medical attention in the various medical facilities. Any device that connects to the internet is always at risk of exposing its data.
Devices like ICDs (Implantable cardioverter defibrillators) are used for protecting patients after being implanted close to their hearts in their bodies. The ICD’s on-board computer is used for keeping track of the patient’s heart rate and then wirelessly relaying this information to a device that is connected to the internet. In case of abnormal heart rhythm, this device will emit small electric shocks that will help in avoiding a cardiac arrest or any other heart trouble. These types of devices have wireless antennas that do not encrypt their data when broadcasting thereby allowing hackers to latch on to them and manipulate it in any other way thereby putting patients and their private data at risk.
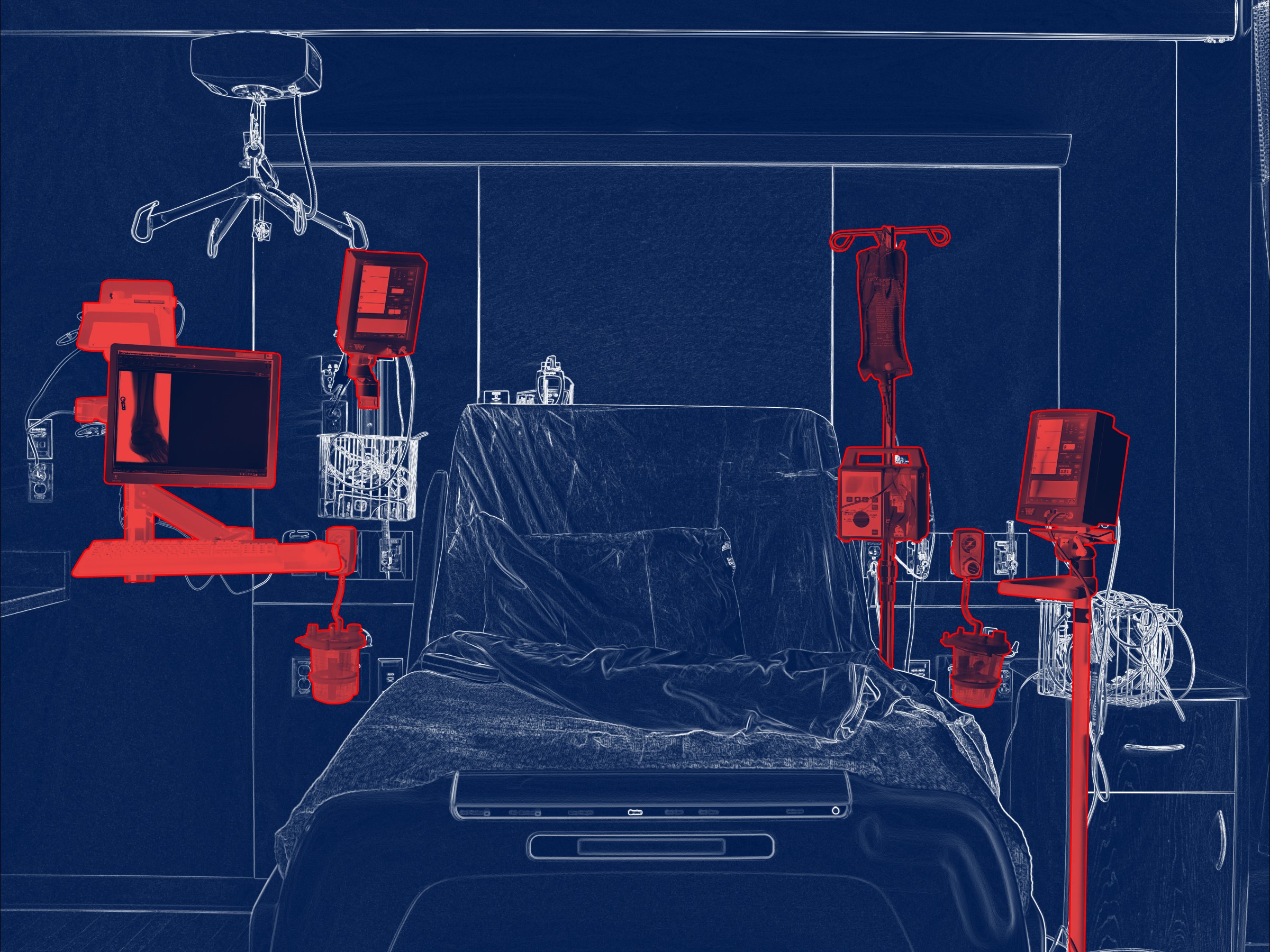
Sometime back, the U.S Food and Drug Administration (FDA) advised hospitals against the use of the Hospira Infusion pump due to a security vulnerability that could allow cyber attackers to gain full remote control of the system. This came a few days after the US Department of Homeland Security issued a warning about the pump’s vulnerability. This pump is used to deliver medications directly into a patient’s bloodstream.
Even after this warning, it is evident that some hospitals are still using this device on their patients. This is despite the fact that there is a risk of unauthorized access by users who are capable of accessing the device remotely; putting them in a position to change the dosage that the pump is meant to deliver. This can, in turn, lead to over-infusion or under-infusion. The legal and personal liability posed by such a breach is enormous!
Ransomware Threat on Medical Devices
Ransomware is a type of malware that basically encrypts everything on your computer’s hard drive and then locks everything behind a password. The attackers will then demand payment from their victims, with a promise of not destroying the files once they have been paid. Ransomware like WannaCry has been known to infiltrate medical centers all over the world, as well as some telecommunication firms and universities by temporarily hobbling their networks. This goes on to show just how unprepared many of these institutions are for a large scale hack of their systems. Trinsic has onboarded several medical clinics in the past two years who had been recent victims of ransomware and have first hand experience with the extenuating HIPPA concerns which effect all aspects of the business.
Most of the medical network-connected equipment in these clinics, hospitals and even doctors’ offices have languished for many years without being replaced or even upgraded. This has led to the emergence of several groups of concerned cybersecurity professionals who are looking into making the case that these older devices have software vulnerabilities that most hackers could easily exploit, and that most of them cannot be salvaged in such cases. The idea is that hospitals should not always wait until these devices stop working for them to be replaced, rather, they should ensure that they are on the lookout for any new security threats or upgrades and take necessary actions in ensuring that the devices are safe at all times.
Ways Of Securing Vulnerable Devices From Hackers
- Disposing Of Old And Vulnerable Devices
For the hospitals to ensure the security of their devices and data in general, the best place to begin will be by getting rid of the unsecured, old devices from their facilities. This is because most hackers today have studied and understood how these devices work and they can easily freeze the systems or even hijack medical records. The life of the patients in such hospitals could at times be dependent on these hackers as they will also be in a position to administer lethal doses of medication via a device like the infusion pump.
This is not to say that the newer devices are perfect or completely safe from hackers, but at least they are typically built with a lot of new and reliable security features that make it hard for the hackers to access. At Trinsic, we strongly encourage our clients to do inventory audits to ferret out devices which need to be replaced and implement a plan to have them replaced.
- Offering Cyber Security Awareness To The Health-Care Industry
There is also a need to offer cybersecurity awareness and education in the health care industry so as to help protect their data and equipment from unauthorized access. For this approach to be successful, all members of the healthcare industry will be required to work together toward the common goal of protecting one another, and most importantly, protecting the patients. Providers should require their IT staff or vendors use the latest tools to identify and quarantine threats. For example, at Trinsic the current threat environment has required us to move well beyond just simple antivirus at the desktop and server level.
Once a common baseline is established between all the parties involved, the industry will be required to come together in order to develop a methodology that will help them to measure, audit, and always help to continuously steer the healthcare industry progressively forward.
Patients will also be required to be aware of how to manage their healthcare data. For this method to remain effective and successful, there should always be thorough ongoing meetings, workshops, tabletop exercises, and conferences.
- Increasing The Resilience And Security Of Medical Devices
The Health Care and Public Health sector, in general, is charged with ensuring the security of patients by protecting them and their information. This means that it should ensure that all devices in the market and in medical facilities adhere to the standards required.
If these devices are exploited, vulnerability may result in malfunction, inappropriate access to patient information, and disruption of health care services. All these will negatively impact patient care and safety and often result in financial loss to providers. A breach will include addressing some foundational changes like maintenance on health care networks, securing development life cycles, improving security processes, etc.
- Information Sharing
Information sharing on the industry’s risks, threats, and mitigation should also be encouraged amongst all the stakeholders. This approach, however, is normally more successful for most organizations that boast already available personnel, resources and infrastructure that help them analyze large amounts of technical information. Unfortunately, for the healthcare industry, most of them are either small or medium-size businesses. This means that they have fewer to zero cybersecurity dedicated experts in their organizations who can take advantage of this constant stream of information that can at times become overwhelming.
For the industry to develop an efficient information sharing system, the government and the healthcare industry will be required to take an approach that will see them engage closely with the many initiatives for sharing information currently underway as they grow and evolve. This should, in turn, work toward ensuring that the best resources are always leveraged from the numerous systems and tailored toward the unique needs of healthcare providers at the same time protecting privacy and maintaining appropriate legal protections.
The solutions must also offer enticements to those in the industry to self report breaches without business threatening penalties. This way, it becomes easier for the small and medium-sized organizations that rely on limited part-time security staff to consume and report on such data.
- Trading Older Devices for New Ones
Another solution will be to find a way of nudging the health-care providers to trade up. An incentive program similar to the “Cash for Clunkers” would encourage most of them to exchange these old devices with the newer ones. This was a federal auto-rebate plan that was aimed at getting rid of gas-guzzling cars from the roads. This program that was under the name “Car Allowance Rebate System”, worked by offering cash to people for them to turn in these types of vehicles. The money could then be used to purchase new fuel-efficient vehicles. Even though the program ended after depleting its allocated budget, a similar method can be applied to health-care providers. This would be by letting them hand in these old machines and then be compensated for them.
The rebates they receive from them would then be used to procure modern devices that are way safer than the ones they are currently holding in their facilities. This will help those hospitals that were built many years ago where malware and ransomware did not exist at the time. Most of these older devices have passwords that cannot be changed, they also run on outdated third-party software, and most of them also are incapable of allowing patches or software fixes to be incorporated into them. As the platform ages, other software bugs also tend to accumulate in these devices.
Fighting Back Against Hackers
The advisory given by the FDA has demonstrated that there is an ongoing effort to ensure that the healthcare industry remains safe from hackers who might turn out to be a very dangerous threat to the rest of the industry.
It is through the combined efforts by security researchers, who continue to provide expertise from a technical perspective to concerned authorities, which result in actions being taken. An example of this was demonstrated by researcher Billy Rios who alerted the Department of Homeland Security on his findings on a number of models of the Hospira Infusion pump that ran a risk of being digitally manipulated. This warning was then later communicated to the FDA, which later issued an advisory in 2015 warning hospitals against the use of such pumps.
Prior to this action, it was very hard for such warnings or advice from experts to be heeded. IT staff should be encouraged to report breaches but must do so in a responsible manner as to insure they are staying within regulatory guidlelines and insuring their actions do not adversely impact the business for whom they work.
The Role of IT
Hackers will continue to threaten the healthcare industry as the information (both monetary and personal) can be utilized for their own financial gain. According to Cybersecurity Ventures, ransomware damages reached $5 billion in 2017. At Trinsic, we realize our client’s expect us to do more than the regulatory minimum to protect their data. The fact is the greatest cost of a breach is often not the regulatory fine but instead the loss of business through the consumer’s response to knowledge of a breach.
It is imperative IT professionals stay vigilant by using the latest detection technology, updating and patching security holes which are exposed from routine audits and working with clients to insure knowledge of their internal processes and procedures.
The healthcare industry is unique and utilizes hardware and software that is industry specific. It is important vendors chosen to protect these networks have institutional knowledge of the industry. It is through the use of qualified professionals and crafting a regulatory environment which benefits patients and providers that success will ultimately be achieved.